Why Switch to Palo Alto Networks' ML-Powered Next-Generation Firewalls
In simple terms, the internet is becoming increasingly dangerous for businesses. Hackers are getting smarter and finding new ways to steal information and cause problems. Traditional security tools aren't enough to protect against these threats.
Palo Alto Networks is a company that helps businesses stay safe online. They have a special firewall that uses artificial intelligence (AI) to identify and block dangerous attacks. This firewall, along with other cloud-based tools, provides strong protection against even the most advanced cyber threats.
This guide will explain how Palo Alto Networks works, the advantages it offers, and why it's a valuable tool for businesses that want to improve their security.
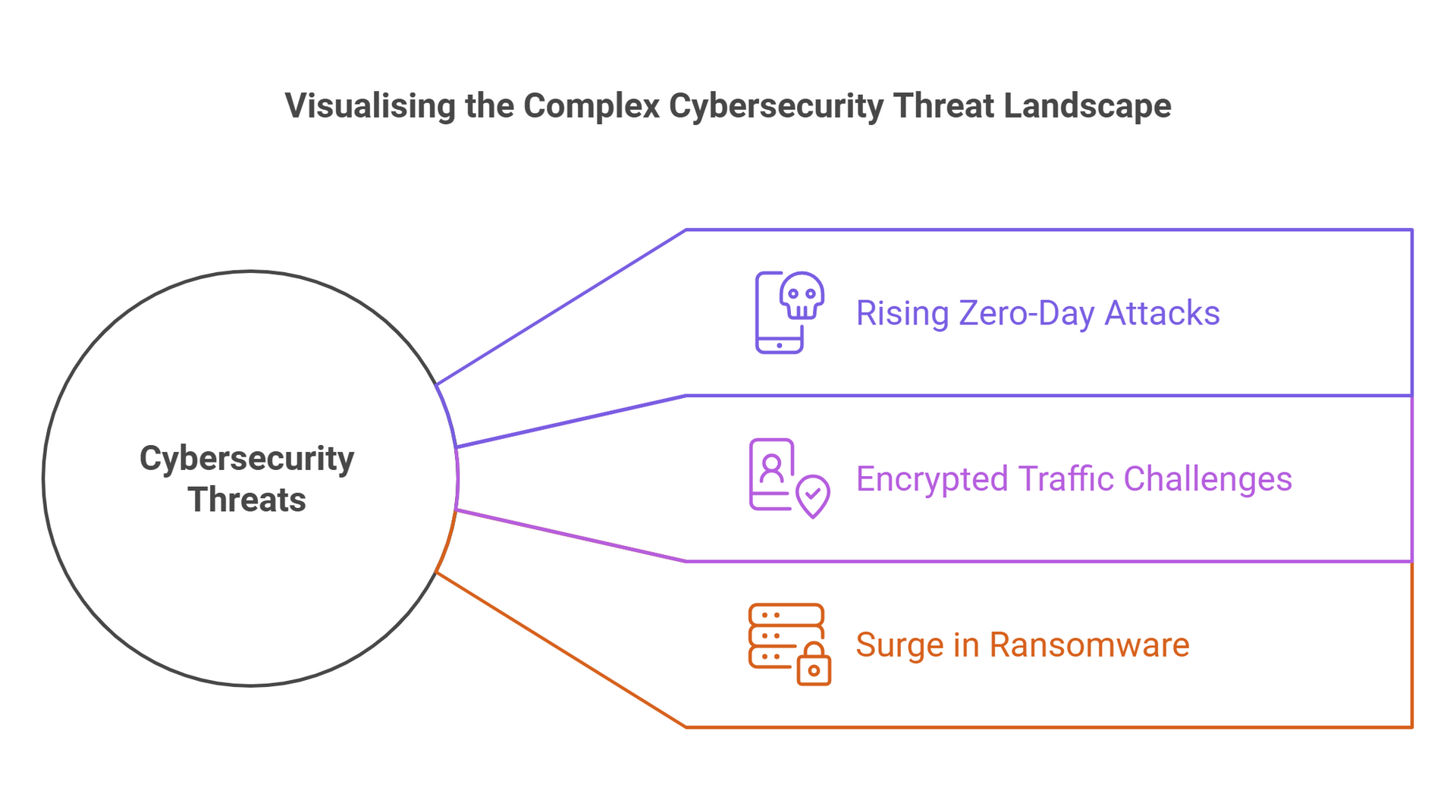
Understanding the Cybersecurity Landscape
Cybersecurity threats are growing both in scale and complexity. A few alarming trends underscore the urgency for advanced solutions:
- Zero-Day Attacks: These are attacks that exploit weaknesses in software that haven't been discovered yet. They're very hard to detect and can cause serious damage. In 2021,
66 zero-day exploits were recorded, highlighting the increasing sophistication of attackers.
- Encrypted Traffic: Over 90% of internet traffic is now encrypted, which is good for privacy but bad for security. Hackers can hide malicious activity within this encrypted traffic, making it difficult for traditional security tools to spot.
- Ransomware Attacks: These attacks lock up a company's data and demand payment to unlock it. Ransomware attacks are becoming more common with a reported 13% increase in 2023, and the ransom demands are getting higher.
Organisations need solutions that can stay ahead of attackers by detecting, analysing, and mitigating threats before they cause damage.
What is Palo Alto Networks ML-Powered NGFW?
At the heart of Palo Alto Networks' offerings is the
ML-Powered Next-Generation Firewall (NGFW)—a transformative approach to cybersecurity. This isn’t just a traditional firewall; it’s an intelligent, AI-driven solution designed to identify and prevent threats in real time.
Challenges Driving Innovation
- Hackers use malware algorithms often to target one computer and then spread their attacks to other devices. Older security systems either take too long to update their defenses or slow down everything by checking every single file.
- Hackers create entirely new malware that needs and firewalls need more rapid response to detect and block, and quickly update defenses once a new threat has been identified.
- More and more internet-connected devices, like cameras and smart appliances, are being added to business networks. This makes it harder to keep them secure. Imagine a new camera that starts sending files to another network. Older security systems can't always detect this kind of unusual activity.
- It's hard for security experts to keep up with all the new devices, apps, and cyberattacks. Security rules are often set loose or less restrictive to keep up, which can leave the network vulnerable.
Key Features of Palo Alto Networks' ML-Powered NGFW
1. Real-Time Threat Prevention
- Detects and blocks threats instantly, including zero-day attacks, evasive malware, and advanced persistent threats (APTs).
- Integrates inline machine learning, allowing the firewall to analyse and block malicious files during downloads in real-time.
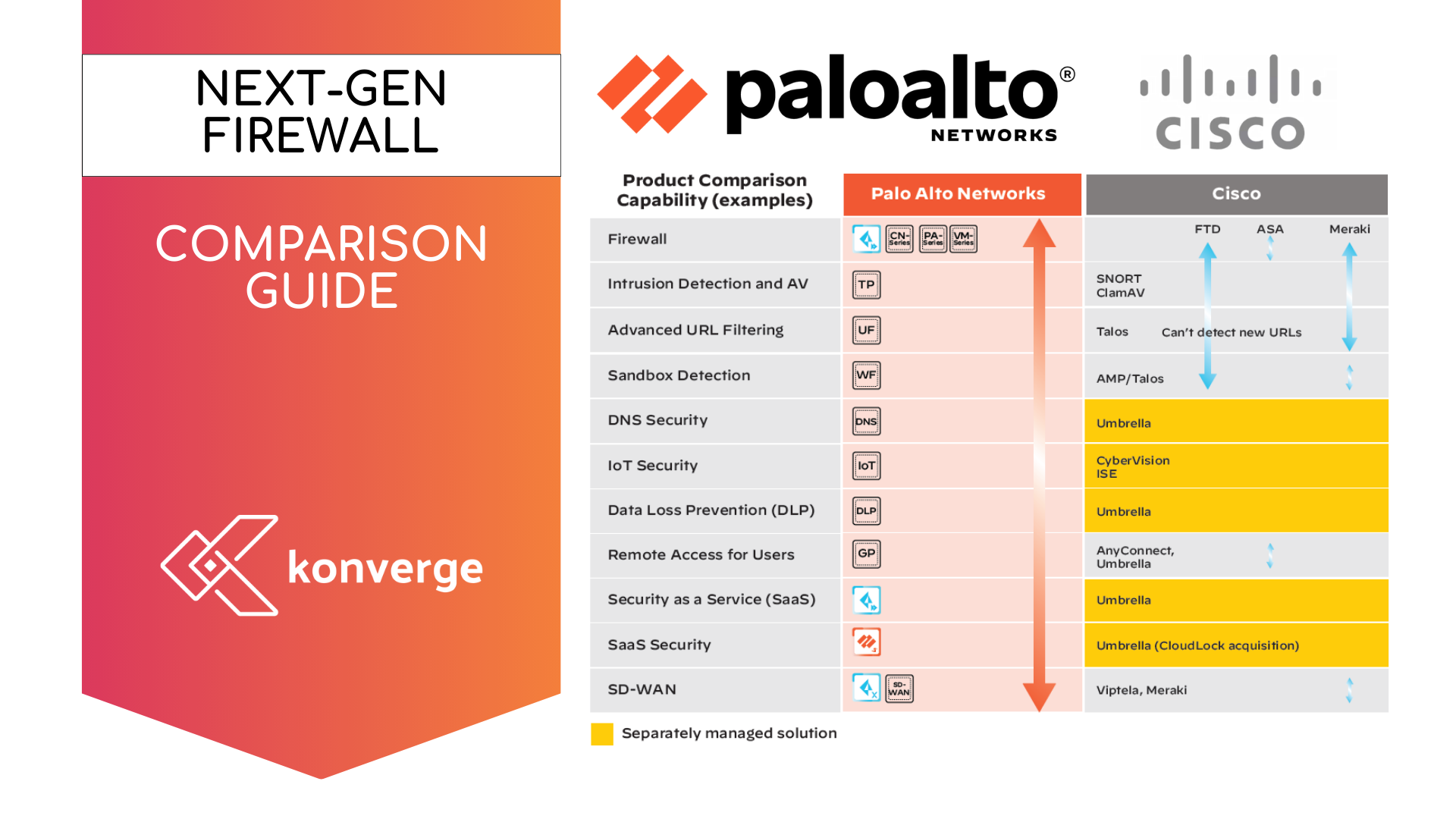
2. Integrated Cloud Services
- Works seamlessly with cloud-delivered services such as
Advanced Threat Prevention,
DNS Security, and
Advanced WildFire to enhance threat detection and prevention.
- Provides unified protection against threats across multiple vectors, including network, endpoint, and cloud.
3. Decryption Capabilities
- Inspects encrypted traffic, including SSL/TLS streams, without impacting privacy or network performance.
- Uncovers threats concealed within encrypted communications, which are often exploited by attackers.
4. Single-Pass Architecture
- Processes all security functions in one go, ensuring high performance and minimal latency.
- Reduces the computational burden on the network, maintaining efficiency even with multiple features enabled.
5. Context-Aware Security
- Employs technologies like
App-ID and
User-ID to enforce granular policies based on applications, users, and devices.
- Enables dynamic, adaptive security policies aligned with Zero Trust principles.
6. Scalability
- Offers flexible deployment options, including hardware appliances (PA-Series), virtual appliances (VM-Series), and cloud-delivered solutions (Prisma Access).
- Adapts to the unique needs of organisations of all sizes and industries.
7. Inline Machine Learning
- Embeds ML algorithms directly into firewall operations, enabling
immediate analysis and prevention of threats.
- Provides zero-delay signature updates after analysis, blocking future mutations of detected threats.
8. ML-Powered IoT Visibility
- Automatically identifies and monitors IoT devices, classifying behaviours to detect anomalies and potential threats.
- Offers detailed insights without requiring predefined device definitions.
9. Automated Policy Recommendations
- Analyses network activity to suggest optimized security policies.
- Reduces manual intervention and minimizes configuration errors, simplifying the management process.
Unified Cloud-Delivered Services
In addition to the
ML-Powered NGFW, Palo Alto Networks offers a comprehensive suite of cloud-delivered services that enhance its security framework. These include:
- Advanced Threat Prevention: Combines inline machine learning with intrusion prevention and malware blocking.
- Advanced URL Filtering: Prevents access to malicious websites and stops phishing attacks in real time.
- Advanced WildFire: Utilizes global threat intelligence and machine learning to prevent unknown threats.
- DNS Security: Disrupts DNS-based attacks and provides visibility into DNS-layer activity.
- IoT Security: Identifies, segments, and secures IoT devices, integrating seamlessly into the NGFW.
Comprehensive Benefits of Software Subscriptions
Why Organisations Choose Palo Alto Networks
1. Enhanced Visibility and Control
The
Application Command Center (ACC) provides real-time insights into network traffic, user activity, and threats, enabling smarter and faster decision-making.
2. Cost-Effective Security
Palo Alto Networks consolidates multiple security functions into one integrated platform, eliminating the need for standalone tools and reducing operational costs.
3. Scalability and Flexibility
The ML-Powered NGFW’s adaptability ensures businesses of all sizes can implement solutions tailored to their unique needs.
4. Proactive Defense
By leveraging ML and AI, Palo Alto Networks delivers proactive threat prevention, addressing risks before they materialise.
The latest ML-Powered NGFWs bring industry-leading performance and security to emerging use cases
These new platforms are much faster than older models. This means they can stop even the most advanced cyberattacks and protect every part of your business, no matter how big or small.
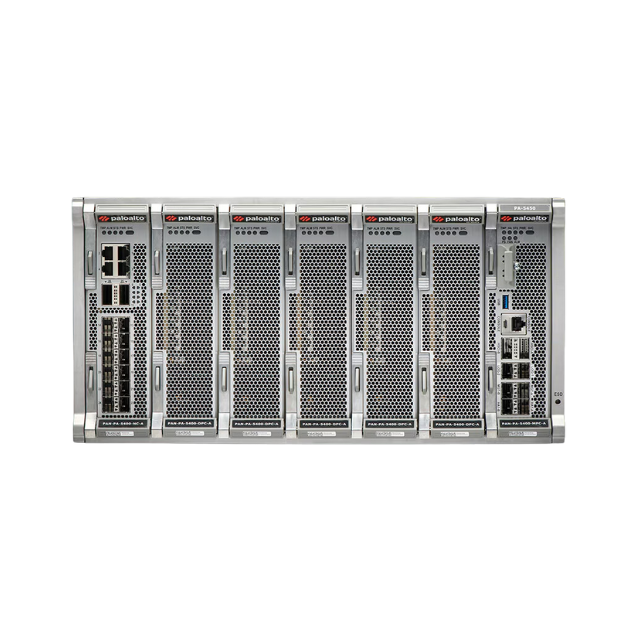
PA-7500 SERIES
PA-7000 SERIES
PA-5450 SERIES
PA-5400 SERIES
PA-3400 SERIES
PA-1400 SERIES
PA-400 SERIES
PA-400R SERIES
Why Switch to Palo Alto Networks?
Palo Alto Networks’ ML-Powered NGFW represents the future of cybersecurity. By embedding machine learning, integrating advanced services, and enabling real-time threat prevention, it provides organisations with unmatched security capabilities.
Switching to Palo Alto Networks isn’t just about upgrading your defenses—it’s about transforming your approach to cybersecurity. With their innovative solutions, businesses can protect critical assets, adapt to evolving threats, and confidently navigate the digital age.
Don’t wait for the next breach. Elevate your security today with Palo Alto Networks.