CPS 234 Gap Audit: 3 Hidden Failures APRA Just Flagged – And How to Fix Them
CPS 234 Gap Audit: 3 Hidden Failures APRA Just Flagged – And How to Fix Them

In today’s hyper‑connected world, cyber security is no longer a niche concern for banks and insurers—it is a universal business imperative. The Australian Prudential Regulation Authority (APRA) recognised this when it introduced Prudential Standard CPS 234 on information security. CPS 234 requires APRA‑regulated entities to maintain “prevention, detection and response capability” to withstand cyber attacks.
Over the past two years, APRA has embarked on a tripartite audit program to test how well institutions are meeting the standard.
The results have been sobering. In the first tranche of audits, APRA found that roughly 24 percent of regulated entities were assessed and identified a string of “common control gaps”.
These gaps reveal hidden failures in many organisations’ cyber defence strategies, leaving them vulnerable to breaches, regulatory penalties and reputational damage. As a security‑focused systems integrator and managed services provider, Konverge Australia sees these failures first hand. We help mid‑sized and enterprise‑scale organisations close the gaps and build cyber‑resilience through vigorous processes, technology and expertise.
This article unpacks the top three hidden failures flagged by APRA, including asset classification, third‑party control assurance and control testing programs, and offers practical guidance on how to address them. By understanding the pitfalls and implementing a structured remediation strategy, organisations can transform compliance into a competitive advantage.
Hidden Failure 1 – Incomplete Identification and Classification of Information Assets
Why It Matters
Information assets are the lifeblood of modern organisations—your customer data, core banking systems, payroll platforms and intellectual property. CPS 234 requires that all critical and sensitive assets be identified, classified and protected accordingly. APRA’s audits, however, revealed that many institutions lack comprehensive asset inventories and have no clear criteria for defining what constitutes a “critical” or “sensitive” asset.. In some cases, third‑party‑managed assets weren’t identified at all.
When assets aren’t properly classified, it becomes impossible to apply the appropriate security controls. Important data may sit on unpatched servers, while non‑critical systems get unnecessary protections. Regulators also expect detailed evidence of how assets are managed; incomplete registers make compliance audits painful and expensive.
What Organisations Are Doing Wrong
Through our consulting work we’ve seen common missteps:
- Static spreadsheets – Organisations often maintain asset lists in static spreadsheets that aren’t tied to any change‑management process. As soon as a new application is deployed or a virtual machine spun up in the cloud, the register becomes outdated.
- No classification criteria – Teams struggle to agree on what counts as “critical” because they lack a structured impact‑assessment framework. Without clear criteria, classification becomes subjective and inconsistent.
- Limited visibility into third parties – Vendors and cloud providers hold and process a growing share of sensitive data, but their assets are often invisible to internal registers. This is especially common with Software‑as‑a‑Service (SaaS) applications that are purchased directly by business units.
How to Fix It
- Build an integrated Configuration Management Database (CMDB): APRA recommends using a central information asset inventory repository such as a CMDB to facilitate registration and mapping of interrelationships. A CMDB should be automatically fed by your infrastructure‑as‑code tools, cloud management platform and IT service management (ITSM) system. Changes should trigger updates in near‑real time.
- Define criticality and sensitivity criteria: Work with business owners to build a scoring matrix that assesses the potential impact of a compromise (confidentiality, integrity, availability and regulatory consequences). Assets should inherit the highest criticality and sensitivity ratings of their constituent components. Document these criteria in policy and embed them in asset‑onboarding workflows.
- Extend visibility to third parties: Require vendors to provide detailed asset inventories and classification evidence. Where possible, federate or integrate third‑party CMDB data into your own repository. If you rely on SaaS services, maintain an internal catalogue of apps, owners, data types and underlying infrastructure locations.
- Assign asset owners and review periodically: Each asset or service should have a responsible owner accountable for classification accuracy and ongoing review. Schedule periodic audits to reconcile your asset inventory with reality. Automated discovery tools can highlight discrepancies and trigger remediation tasks.
- Leverage managed services: If your team lacks the resources to maintain a CMDB and classification program, consider partnering with a specialist provider like Konverge. We deploy tools, processes and expertise to build sustainable asset management frameworks.
By taking these actions, organisations can move from fragmented asset lists to a dynamic, holistic view of their environment. This is the foundation for all other CPS 234 controls, including risk assessment, access management and incident response.
Hidden Failure 2 – Insufficient Assurance of Third‑Party Information Security Controls
Why It Matters
Modern businesses are intricately connected ecosystems. Cloud platforms, outsourced call centres and software vendors all operate parts of your critical technology stack. APRA’s audits found that organisations rarely have comprehensive plans to assess third‑party security controls, and often rely solely on self‑attestations from vendors. Evidence of control testing is not always retained, and the scope of testing doesn’t align to the criticality of the data.
A single weak link in the supply chain can expose your company to a data breach or service disruption. Regulators are increasingly scrutinising third‑party risk, requiring that contracts include clear notification obligations for security incidents and that organisations can demonstrate due diligence. Failure to manage vendor risk can lead to fines, lawsuits and reputational damage.
Common Missteps
- Contractual gaps – Many contracts don’t require vendors to notify the organisation of material security incidents or allow for independent audits.
- Over‑reliance on compliance certificates – SOC 2, ISO 27001 or CSA STAR certifications are valuable but do not guarantee that controls are effectively implemented for your specific environment.
- Lack of contextual testing – Testing is not tailored to the criticality of the data being handled. For example, a vendor handling personal health data may only be asked to complete a generic questionnaire.
- Poor evidence management – Control testing results are not retained, making it difficult to prove due diligence during audits.
How to Fix It
- Map your vendor ecosystem: Start by identifying which information assets are managed by third parties. This mapping determines the level of rigour required in assessments.
- Integrate security clauses into contracts: Every contract should specify requirements for security controls, right‑to‑audit, notification of incidents and control weaknesses, and compliance with CPS 234. Include the requirement for prompt reporting to APRA when applicable.
- Develop a tiered vendor‑risk assessment model: Not all vendors pose equal risk. Segment them based on the sensitivity of the data and criticality of the service. High‑risk vendors should undergo detailed control testing, including on‑site audits and penetration testing; low‑risk vendors might suffice with a self‑assessment and certificate review.
- Use a combination of evidence sources: APRA recommends assessing third‑party controls through interviews, surveys, control testing, certifications, contractual reviews, attestations and independent assurance. A mix of qualitative and quantitative evidence provides a more accurate picture.
- Retain testing evidence:
Store evidence of control design, operation and effectiveness in a central repository that can be produced during audits. This includes penetration test reports, vulnerability scans, SOC reports and policy documents.
- Continuous monitoring: Implement tools to monitor vendors’ security posture and data flows in real time. This may include security‑rating services, API‑based monitoring of SaaS applications and periodic questionnaire re‑assessments.
- Engage independent assessors: Where internal expertise is limited, engage independent experts or managed service providers like Konverge to design and execute vendor‑risk assessments. External assessors bring objectivity and specialised tooling.
By formalising vendor‑risk management, organisations can demonstrate to regulators and customers that they are proactively managing their digital supply chain. This not only reduces the risk of breaches but also builds trust with stakeholders.
Hidden Failure 3 – Inadequate Definition and Execution of Control Testing Programs
Why It Matters
Control testing is the mechanism by which organisations verify that security controls are effective and remain so as the environment evolves. APRA requires entities to systematically test the effectiveness of information security controls. Yet many organisations do not have comprehensive testing programs; testing lacks independence, lacks coverage of key controls and fails to retain evidence.
Without a robust testing program, management and boards operate in the dark. Controls may exist on paper but may not work in practice. Attackers exploit misconfigurations, outdated protocols and lapses in monitoring. Ineffective testing can lead to unaddressed vulnerabilities, resulting in breaches or regulatory breaches.
Common Pitfalls
- Inconsistent scope and frequency: Testing is sometimes sporadic or limited to narrow control sets, ignoring user access reviews, physical security, data loss prevention and other critical controls.
- Lack of independence: Controls are often tested by the same teams that implemented them. This undermines objectivity and reduces the likelihood of uncovering weaknesses.
- No clear success criteria: Without predefined criteria, testing becomes subjective and results are difficult to compare over time.
- Poor evidence retention: Evidence of testing—such as logs, screenshots and reports—is not archived, making it hard to prove compliance to auditors.
How to Fix It
- Develop a formal control‑testing strategy: Document a program that defines the testing methods (e.g., control self‑assessment, independent testing, red teaming), frequency and scope. APRA suggests adopting a variety of testing approaches.
- Establish clear success criteria: For each control, define the desired outcome and threshold for passing or failing. Include criteria for when controls should be re‑tested.
- Ensure functional independence: Controls should be tested by individuals or teams with no operational responsibility for those controls. If internal resources are limited, engage external assessors.
- Prioritise critical controls: Identify controls that protect high‑impact assets—such as privileged access management, encryption, patch management and incident response—and test these more frequently.
- Automate wherever possible:
Use continuous control monitoring tools that automatically test and validate control effectiveness. For instance, privileged accounts can be automatically checked for policy compliance.
- Retain comprehensive evidence: Store test plans, results and supporting artefacts in a secure repository. Evidence retention not only satisfies regulatory requirements but also allows teams to analyse trends over time and demonstrate continuous improvement.
- Report to governance bodies: Summarise testing results and exceptions to management and the board on a regular basis. This fosters accountability and ensures that remediation efforts are prioritised.
An effective control‑testing program turns security controls from “set and forget” into a living system of continuous improvement. When combined with robust asset classification and vendor‑risk management, it forms the backbone of a mature cyber‑security posture.
Beyond the Top Three – Other Gaps in APRA’s Findings
While this article focuses on three critical failures, APRA’s stocktake identified additional weaknesses that organisations must address to achieve full CPS 234 compliance. These include:
- Incident Response Plans: APRA found that many entities either lack incident response plans or fail to test them regularly. Plans often do not define roles and responsibilities or cover a broad range of plausible scenarios. Entities should develop detailed playbooks covering malware, data breaches, credential compromise, denial‑of‑service attacks and website defacements, and conduct regular tabletop exercises.
- Internal Audit Reviews: Internal audit teams often
don’t review third‑party controls and may lack the necessary information‑security skills. Boards should mandate that internal audit programs include coverage of cyber controls and provide training or external support where necessary.
- Notification of Material Incidents: Many organisations haven’t established clear processes to notify APRA of material incidents and control weaknesses. APRA expects governance processes to be in place for escalating incidents and reporting them in a timely manner. Contracts with critical third parties should include notification obligations.
Addressing these additional gaps requires cross‑functional collaboration between IT, risk management, legal, procurement and executive leadership. The journey to CPS 234 compliance isn’t a box‑ticking exercise; it’s an ongoing cultural change.
Steps to Achieve CPS 234 Compliance: A Holistic Framework
Achieving and sustaining CPS 234 compliance involves more than implementing a handful of controls. Below is a holistic framework that integrates the hidden failures highlighted earlier with broader best practices:
- Executive Alignment and Governance: Begin by securing board‑level and C‑suite engagement. CPS 234 specifically calls out the need for boards to oversee information security. Establish a security committee, define roles and responsibilities, and integrate cyber risk into enterprise‑risk management.
- Risk Assessment and Gap Analysis: Conduct an enterprise‑wide risk assessment that maps threats to assets and current controls. Use the findings of APRA’s stocktake to benchmark your maturity. Perform a gap analysis against CPS 234 requirements and industry frameworks like ISO 27001.
- Policy and Standards Development: Draft or update policies and standards for information security, asset classification, access management, encryption, logging, incident response and vendor‑risk management. Ensure these are aligned with CPS 234 and incorporate clear criteria, responsibilities and escalation paths.
- Asset Inventory and Classification: Implement the asset management program described in Hidden Failure 1. Use discovery tools and a CMDB, and define criteria for criticality and sensitivity.
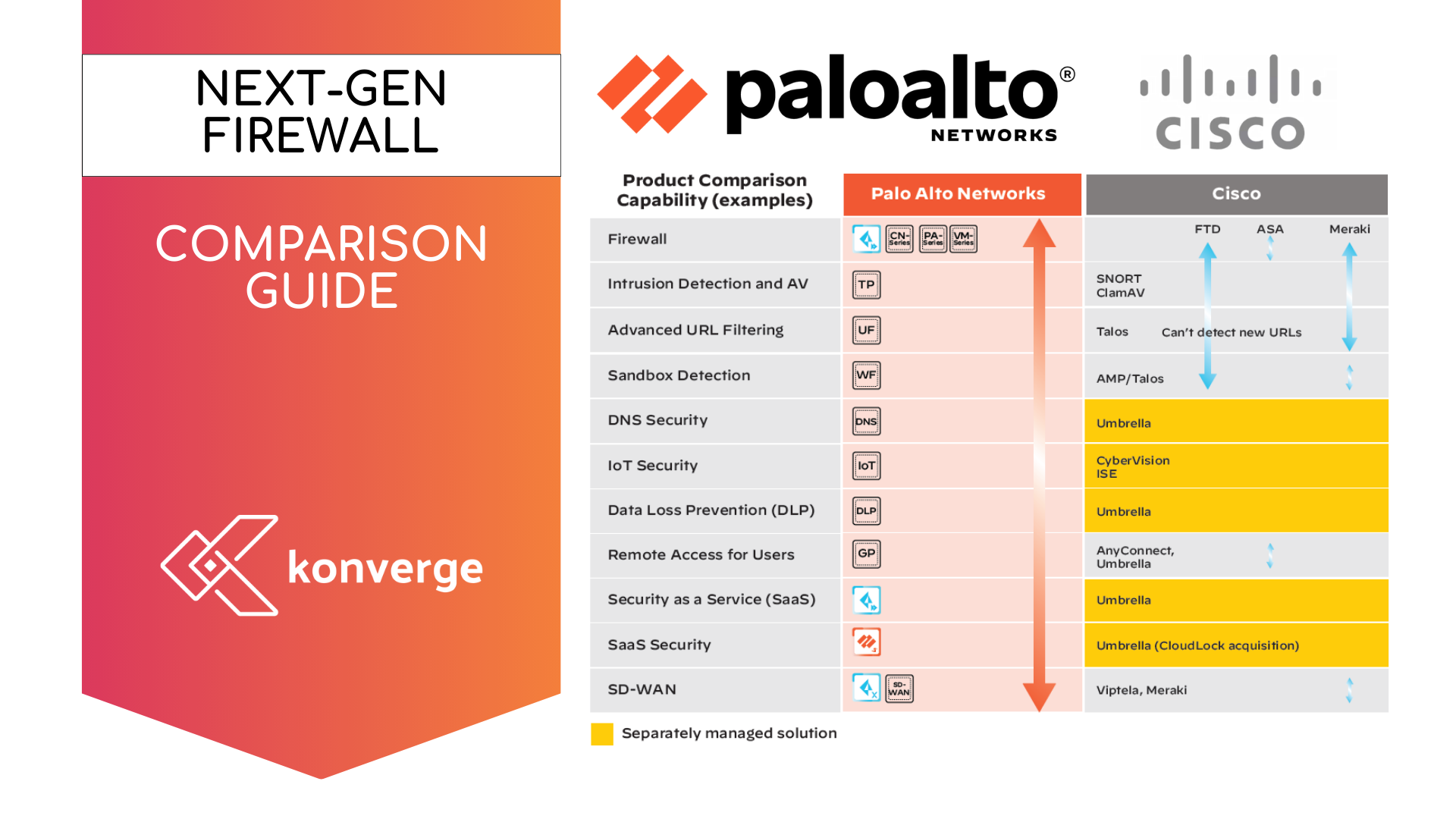
- Control Implementation and Integration: Deploy and configure technical controls such as multi‑factor authentication (MFA), endpoint detection and response (EDR), encryption, network segmentation, and privileged access management. Ensure controls are integrated across on‑premises and cloud environments.
- Third‑Party Risk Management: Follow the recommendations in Hidden Failure 2. Build a vendor inventory, embed security requirements in contracts, and perform tiered risk assessments and testing.
- Control Testing Program: Adopt the testing strategies from Hidden Failure 3. Define a formal testing plan, establish success criteria and ensure independence. Implement automation where possible.
- Incident Response and Business Continuity: Develop detailed incident response and disaster recovery plans. Test them regularly with real‑world scenarios and update them based on lessons learned.
- Training and Awareness: Educate staff at all levels on cyber security, CPS 234 obligations and incident reporting. Regular phishing simulations and awareness campaigns foster a culture of vigilance.
- Monitoring and Continuous Improvement: Implement continuous monitoring of systems, controls and third parties. Use security metrics and dashboards to track progress. Review compliance posture regularly, update controls as threats evolve and incorporate lessons from incidents and audits.
By following this framework, organisations can transform compliance from a reactive checklist into a proactive, resilient system that supports business growth.
How Konverge Australia Can Help
Konverge Australia specialises in designing, deploying and operating secure, scalable and resilient IT environments for mid‑sized and enterprise organisations across high‑trust industries. Our expertise spans security consulting, systems integration, managed services, cloud architecture and procurement.
Here’s how we help you tackle the hidden failures APRA flagged:
- Asset Discovery and Classification: We deploy automated discovery tools to build a real‑time asset inventory and help you classify assets based on impact and sensitivity. Our consultants define scoring models, train your teams and integrate asset management into your ITSM workflows.
- Vendor‑Risk Management: Konverge works with your procurement, legal and risk teams to develop contract templates that embed security requirements. We conduct third‑party assessments, review certifications, perform technical testing and maintain a repository of evidence. Our continuous‑monitoring solutions provide visibility into your vendors’ security posture.
- Control Testing and Assurance: We design comprehensive testing programs that include self‑assessments, independent testing, penetration testing and red teaming. Our experts define success criteria, maintain evidence repositories and present results to boards. We also leverage automation to streamline control validation.
- Incident Response Preparedness: Our incident response consultants help you build playbooks covering the full spectrum of plausible attacks. We conduct tabletop exercises, help tune detection tools and stand by to support you during crises.
- Managed Security Services: If you lack resources to maintain 24×7 security operations, our managed services provide continuous monitoring, threat detection and response. Our team extends your capabilities without the overhead of hiring and retaining scarce cyber‑security talent.
- Training and Awareness: We deliver tailored awareness programs for boards, executives, IT staff and end users. Our training emphasises CPS 234 requirements, real‑world attack scenarios and best practices for secure behaviour.
By partnering with Konverge, you gain a trusted ally to navigate the complexities of CPS 234, reduce risk and turn compliance into a business advantage.
Real‑World Implications – When Gaps Become Breaches
Sometimes the gravity of CPS 234’s requirements is hard to appreciate until things go wrong. Consider the case of a fictional mid‑tier bank, “Aurora Financial,” which delegated its mobile banking platform to a third‑party development house. Aurora kept meticulous records of its on‑premises servers but had no asset register covering the cloud infrastructure its vendor operated. The classification framework was also ambiguous—customer log‑in data was deemed “sensitive,” but session‑tracking logs were not.
When attackers discovered a vulnerability in the vendor’s application programming interface, they gained access to the unclassified session logs and used the information to conduct credential‑stuffing attacks, eventually compromising thousands of accounts. Because Aurora lacked a formal vendor‑risk assessment program, the breach went undetected for weeks. The incident response playbook was limited to internal systems, so no one knew who was supposed to notify APRA or customers. The resulting fallout included a class‑action lawsuit, heavy regulatory penalties and severe reputational damage.
This scenario underscores how the three hidden failures interact. Poor asset classification meant that high‑value data was hidden in “low‑risk” logs; inadequate third‑party assurance allowed the vulnerability to go undetected; and weak testing and incident response programs left the organisation unprepared to detect or contain the breach. It’s a cautionary tale that illustrates why CPS 234 compliance is not just an IT concern but a board‑level priority. Investing in comprehensive asset management, vendor oversight and rigorous testing now can prevent catastrophic losses later.
Turning Compliance into Competitive Advantage
The CPS 234 tripartite audits have exposed critical weaknesses across Australia’s financial services sector. Incomplete asset classification, weak third‑party control assurance and inadequate control testing programs are among the most concerning failures. Addressing these gaps is not merely about ticking regulatory boxes—it’s about protecting your customers, your reputation and your license to operate.
By taking a structured, holistic approach to information security and partnering with experts like Konverge Australia, organisations can move beyond reactive compliance. You can create a culture of security that supports innovation, delivers reliable services and builds trust with regulators and customers. The journey to cyber‑resilience may be complex, but the consequences of inaction are far worse. Start today, and transform CPS 234 compliance into a competitive advantage.